Article
Version 1
Preserved in Portico This version is not peer-reviewed
Cyber-attacks on Public Key Cryptography
Version 1
: Received: 22 September 2023 / Approved: 27 September 2023 / Online: 27 September 2023 (05:29:34 CEST)
How to cite: Radanliev, P. Cyber-attacks on Public Key Cryptography. Preprints 2023, 2023091769. https://doi.org/10.20944/preprints202309.1769.v1 Radanliev, P. Cyber-attacks on Public Key Cryptography. Preprints 2023, 2023091769. https://doi.org/10.20944/preprints202309.1769.v1
Abstract
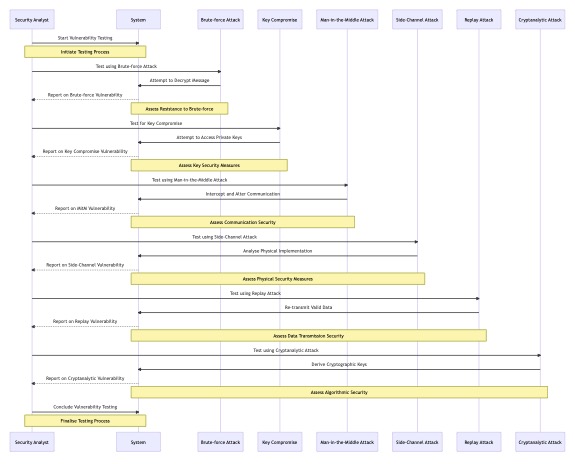
This study provides an in-depth exploration and analysis of the complex aspects of Public Key Cryptography, focusing on the vulnerabilities, potential attack vectors, and the consequential impacts of key compromises. The discussion extends beyond the conventional technical paradigms, offering a holistic perspective that intertwines theoretical insights with practical implications, thereby contributing to a more comprehensive understanding of cryptographic security. The paper delves into the intricacies of brute-force attacks, elucidating the significance of key sizes, encryption algorithms, and the inherent resilience of cryptographic systems against such attacks. It further examines the ramifications of key compromises in Public Key Cryptography, highlighting the repercussions on confidentiality, integrity, trust, and legal and reputational standing. The study underscores the importance of maintaining the security and integrity of cryptographic keys and provides practical recommendations to mitigate the risks associated with key compromises. These include enhanced awareness and education, stringent protection of sensitive information, proactive risk management, strict compliance with regulations and standards, and the promotion of a security-centric culture. The insights gleaned from this study are pivotal in informing future research, policy development, cryptographic implementations, and the cultivation of secure practices, fostering a more secure, resilient, and ethical digital environment in the face of an evolving threat landscape. The contributions of this study are instrumental in advancing the field of cryptography and enhancing the overall understanding of the challenges and considerations inherent in implementing robust cryptographic practices.
Keywords
artificial intelligence; quantum cryptography; quantum computing; security; encryption
Subject
Computer Science and Mathematics, Data Structures, Algorithms and Complexity
Copyright: This is an open access article distributed under the Creative Commons Attribution License which permits unrestricted use, distribution, and reproduction in any medium, provided the original work is properly cited.
Comments (0)
We encourage comments and feedback from a broad range of readers. See criteria for comments and our Diversity statement.
Leave a public commentSend a private comment to the author(s)
* All users must log in before leaving a comment